Continuing our series of technical sharing sessions, VERDESEC hosted another Discord event led by our Trailbl4z3r, this time titled “A Day in the Life as a Malware Analyst.” The session was co-organized with Average Assignment Enjoyer from UTAR and drew an impressive 100 participants, making it one of the most well-received sharing sessions of the year.

The session was designed to give students and aspiring cybersecurity practitioners a closer look at what malware analysis actually involves in practice. While many people are familiar with malware as a concept, fewer have the opportunity to understand the day-to-day work of analyzing suspicious files, identifying malicious behavior, and turning technical findings into malware detection. This sharing aimed to bridge that gap by giving participants an introduction to the field through both explanation and examples.
We began with an overview of what a malware analyst is and the role they play in the wider cybersecurity landscape. Participants were introduced to the responsibilities involved in malware analysis, from examining malicious documents and understanding malicious script to detection engineering based on analysis findings.
To make the session more practical, the sharing also included a malware analysis example. By walking through a sample case, participants were able to see how analysts approach suspicious files, what kind of indicators they look for, and how technical observations can be used to understand a malware sample’s purpose and behavior. This practical element helped make the topic more approachable, especially for students who were new to malware analysis.
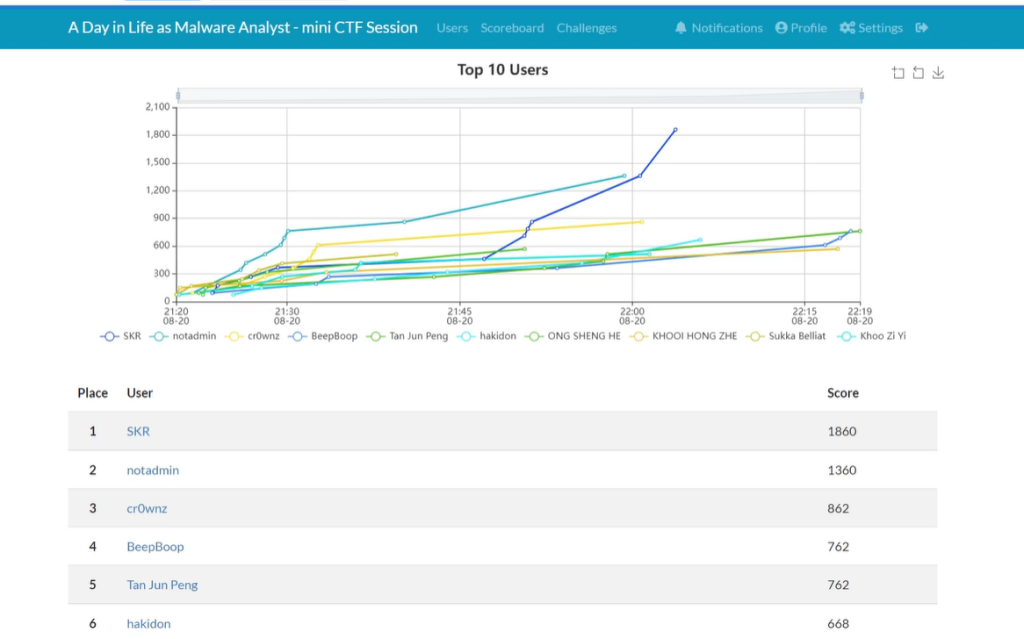
To make the event even more engaging, the session was followed by a small CTF prepared specifically for participants. This added a hands-on component to the experience, allowing attendees to put their curiosity and problem-solving skills to use in a fun and interactive way after the talk. It also helped reinforce VERDESEC’s belief that practical activities are one of the best ways to deepen learning.
By combining technical sharing with interactive challenges, we continue to create opportunities for students to explore cybersecurity beyond the classroom.
| Activity Details: | |
|---|---|
| Venue: | Online |
| Price: | FREE |
| Participants: | 100 |
| Level: | Intermediate |
